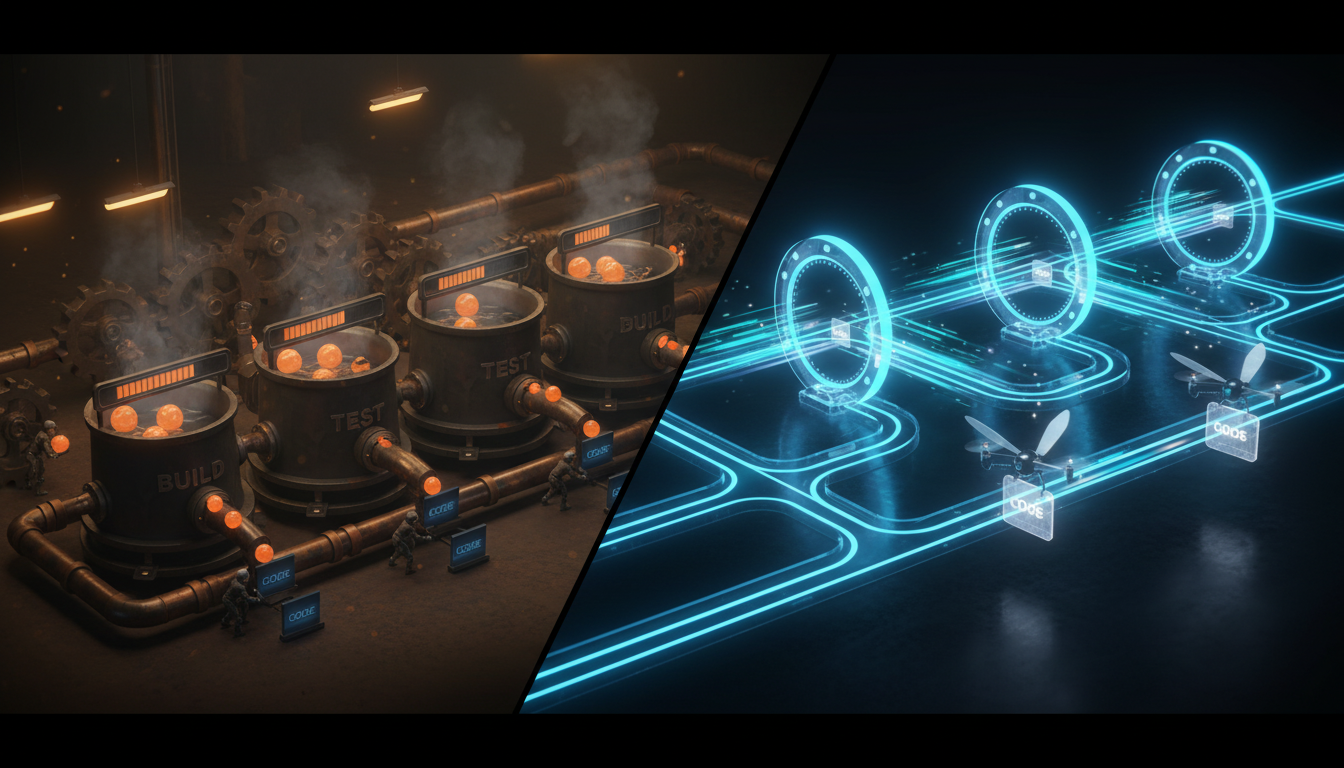
Analytics sandboxes are the R&D labs of your data world: they fuel innovation, enable forecasting experiments, and empower analysts. However, they can feel risky when safeguards lag behind business needs. Security leads and data platform architects face a tough choice: enable freedom to explore or enforce strict controls but slow insights. Many organizations still struggle with ill-defined, under-governed sandbox environments, creating exposure points for sensitive data and compliance challenges.
At Stellans, we promote a better approach: a secure, platform-agnostic analytics sandbox setup that unlocks creativity while reducing risk. Below, we outline actionable best practices to help you design and operate sandboxes that drive accurate forecasting with controls aligned with frameworks like NIST SP 800-53 Rev. 5, ISO/IEC 27001, and EU data protection.