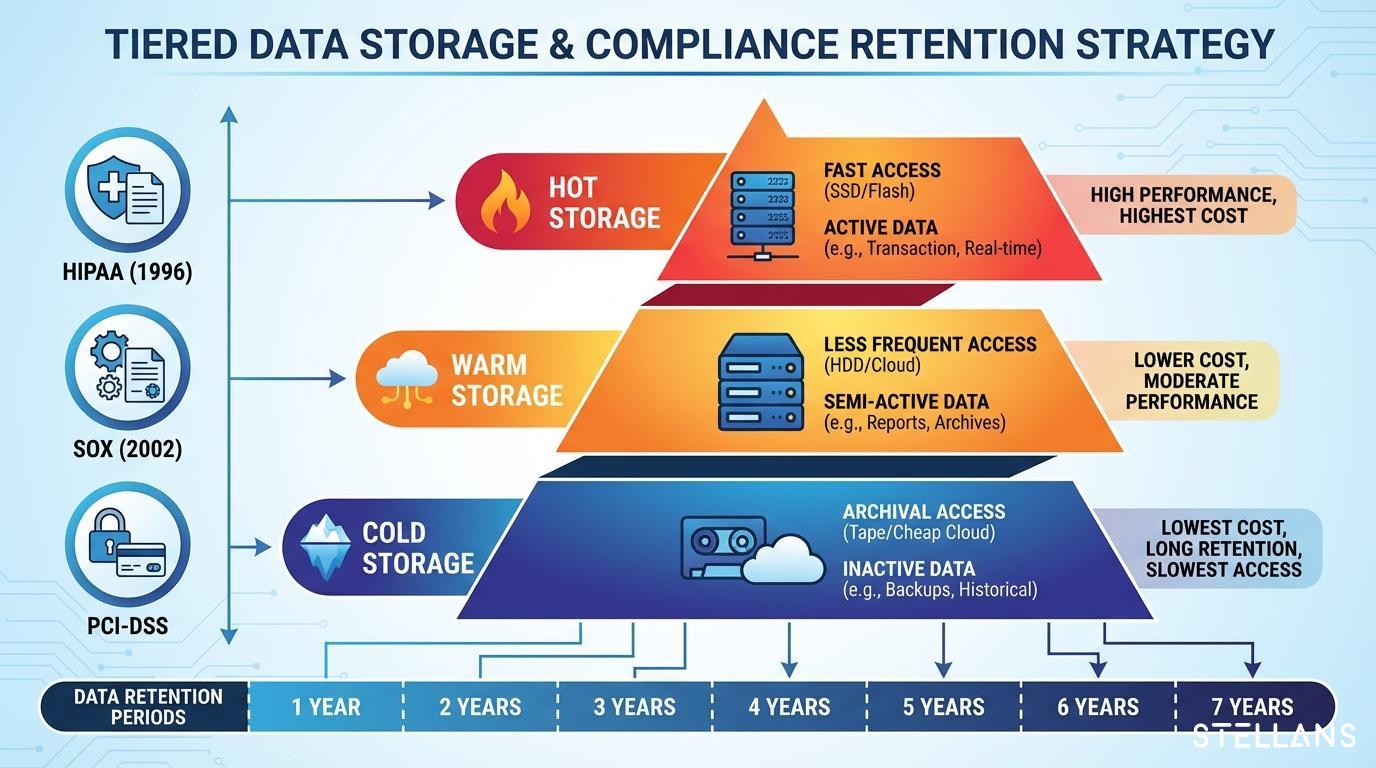
Different regulations mandate different retention periods, and organizations subject to multiple frameworks must design policies that satisfy the strictest requirements. The following breakdown covers the major compliance frameworks affecting data platforms.
HIPAA: 6-Year Minimum for PHI Systems
The Health Insurance Portability and Accountability Act (HIPAA) Security Rule requires covered entities and business associates to retain documentation of security policies and procedures for six years from the date of creation or last effective date. This includes audit logs that track access to protected health information.
Key HIPAA logging requirements include:
- User authentication events
- Access to electronic PHI
- Changes to security configurations
- System activity reviews
SOX (Sarbanes-Oxley): 7-Year Financial Records Retention
The Sarbanes-Oxley Act, enforced by the SEC, requires public companies to retain audit records relevant to financial statements for seven years after the auditor concludes the audit or review. This applies to logs documenting access to financial systems and databases containing material financial information.
SOX audit trails must capture:
- Access to financial reporting systems
- Changes to financial data and reports
- User provisioning and role assignments
- System modifications affecting financial controls
PCI-DSS 4.0: 12 Months with 3-Month Immediate Access
The Payment Card Industry Data Security Standard version 4.0 requires organizations handling cardholder data to retain audit log history for at least 12 months, with at least three months immediately available for analysis. This shorter retention period reflects the time-sensitive nature of payment fraud investigations.
PCI-DSS logging must capture:
- All access to cardholder data environments
- Authentication attempts (successful and failed)
- Actions by privileged users
- Security event alerts
SOC 2: Risk-Based Retention Framework
SOC 2 does not prescribe specific retention periods. Instead, it requires organizations to establish and follow documented retention policies based on risk assessment and operational needs. Most SOC 2 auditors expect organizations to retain security logs for at least one year, though periods of 90 days to three years are common depending on the trust services criteria being evaluated.
GDPR: Data Minimization vs. Security Needs
The General Data Protection Regulation presents particular challenges since it requires data minimization, meaning personal data should not be kept longer than necessary. Organizations must balance this requirement against legitimate security needs for maintaining audit trails. The key is documenting retention justifications and ensuring logs containing personal data are protected accordingly.
ISO 27001 and NIST CSF: Principles-Based Approach
ISO 27001 and the NIST Cybersecurity Framework do not mandate specific retention periods. Instead, organizations must define and implement log retention policies appropriate to their risk profile. NIST SP 800-92, the Guide to Computer Security Log Management provides detailed guidance on log management best practices including retention policy development.
Regulation Retention Period Matrix
| Regulation |
Minimum Retention |
Log Types Required |
Key Requirements |
| HIPAA |
6 years |
PHI access, authentication, and security events |
Must cover all ePHI systems |
| SOX |
7 years |
Financial system access, data changes |
Applies to public companies |
| PCI-DSS 4.0 |
12 months |
Cardholder data access, auth events |
3 months immediately accessible |
| SOC 2 |
Risk-based (typically 1 year) |
Security events, access logs |
Must align with trust criteria |
| GDPR |
Justify and document |
Personal data processing activities |
Balance security vs. minimization |
| ISO 27001 |
Define per policy |
Security-relevant events |
Risk-based determination |